New GPU Attacks: GDDRHammer and GeForge Explained
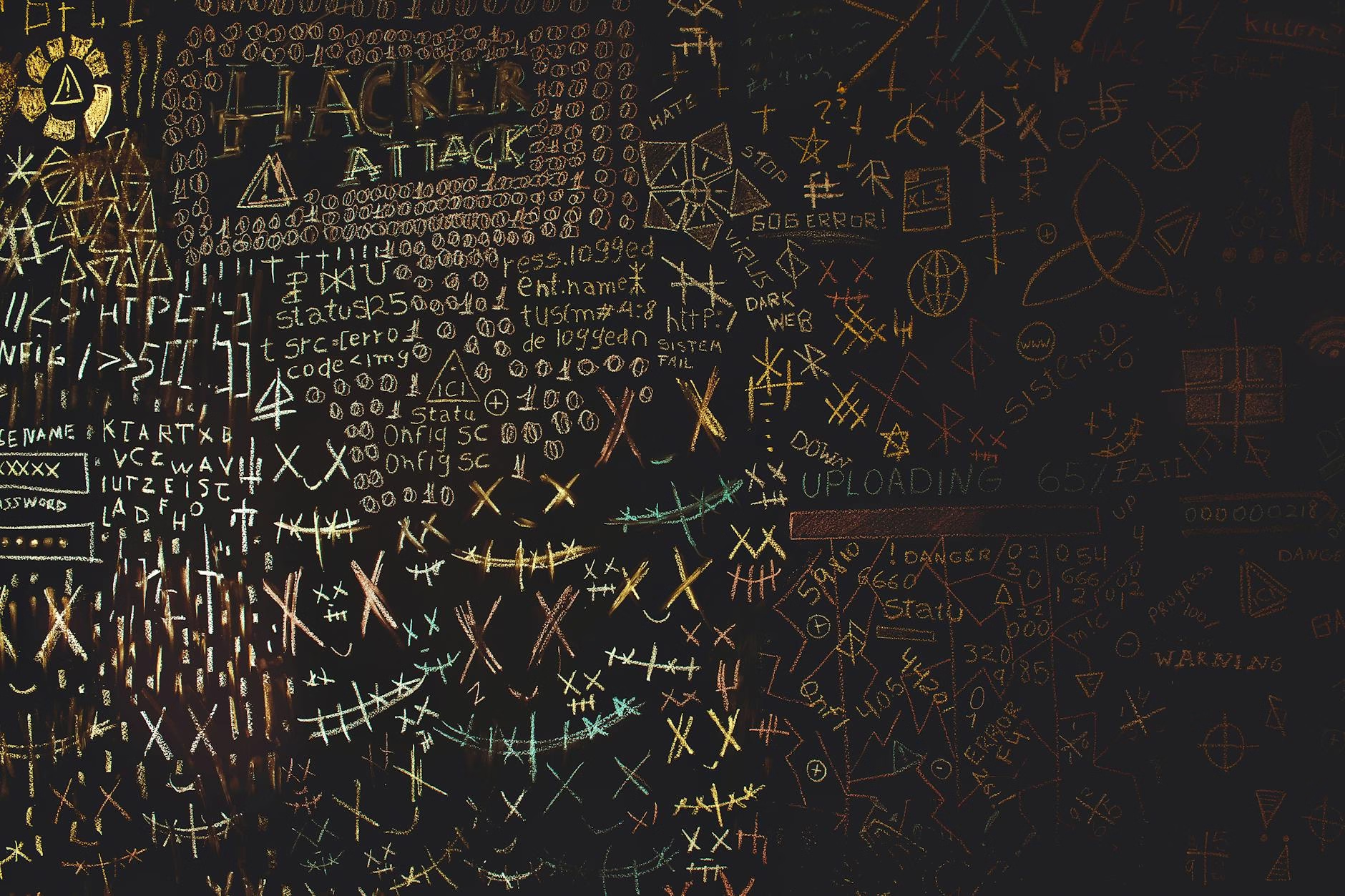
Recent research has unveiled alarming vulnerabilities in high-performance GPUs from Nvidia. The new attacks, named GDDRHammer and GeForge, exploit weaknesses in GPU memory. These findings highlight significant security risks for cloud environments where expensive GPUs are often shared among multiple users.
Understanding the Attacks
The GDDRHammer attack targets Nvidia’s Ampere generation GPUs. It manipulates memory in ways that can compromise the CPU of the host machine. This is particularly concerning because it allows malicious users to gain full root control over systems.
Both attacks leverage a phenomenon known as Rowhammer. This occurs when rapid access to specific memory rows causes electrical disturbances, leading to bit flips. These bit flips can change stored data from 0s to 1s or vice versa, creating vulnerabilities.

How GDDRHammer Works
The GDDRHammer attack uses advanced hammering patterns to induce an average of 129 bit flips per memory bank. This is a significant increase compared to previous methods. By breaking isolation of GPU page tables, attackers can read and write data stored on the GPU.
Andrew Kwong, co-author of the research paper on GDDRHammer, emphasized that this method shows how Rowhammer poses a serious threat not just on CPUs but also on GPUs. Existing mitigations fo
r CPU Rowhammer attacks may not protect against these new threats targeting GPUs.
GeForge: A Similar Threat
The second attack, GeForge, operates similarly but focuses on manipulating last-level page directories instead of page tables. This method was able to induce even more bit flips—1,171 against the RTX 3060 and 202 against the RTX 6000.
Both GDDRHammer and GeForge demonstrate that attackers can breach confidentiality and integrity across different contexts within a system. They manipulate GPU address translation to escalate privileges on Linux systems.
Key takeaways
- GDDRHammer and GeForge exploit vulnerabilities in Nvidia GPUs.
- These attacks allow full control over host CPU memory.
- Existing CPU mitigations may not protect against GPU threats.
- Rowhammer techniques have evolved significantly over the past decade.
FAQ
What are GDDRHammer and GeForge?
They are new attacks targeting Nvidia GPUs that exploit Rowhammer vulnerabilities to gain control over host systems.
How do these attacks work?
The attacks manipulate memory access patterns to induce bit flips in GPU memory, allowing unauthorized access to CPU memory.
Why is this a concern for cloud environments?
The high cost of GPUs often leads to sharing among users in cloud settings, increasing the risk of exploitation by malicious actors.
Sources
For the original report, see the source article.